Cybersecurity Training Videos
Cybersecurity Training Videos
Your employees serve as your front line to protect your company's data. Think about the cost in time and resources with just one breach. Learn how to surf the internet safely, create effective passwords, avoid phishing scams and protect your data with our cybersecurity training videos.
View snippets of these courses below.
Connect with Us Request Free Trial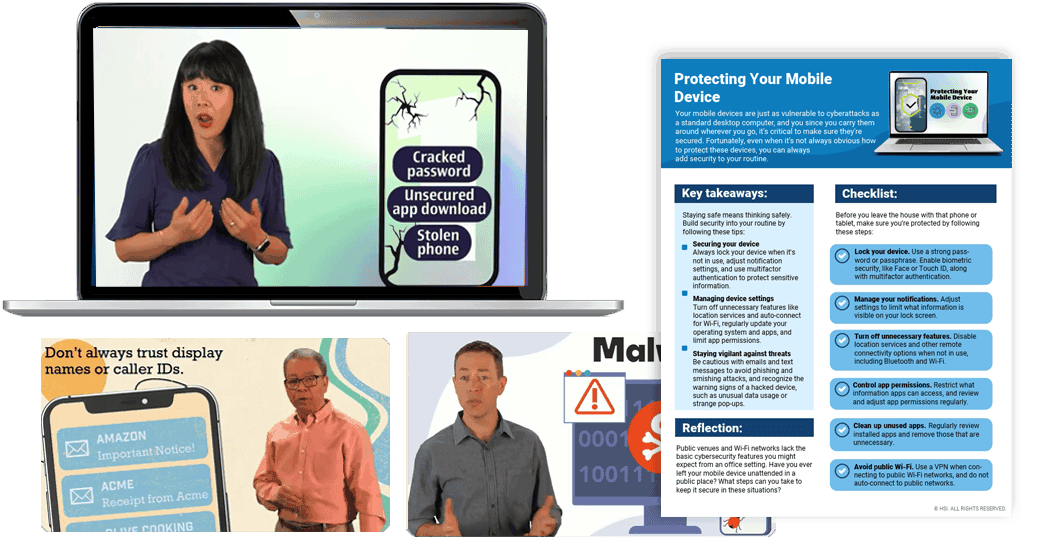
Why HSI for Cybersecurity Training Courses?
Training your employees on cybersecurity is critical in this age of online everything. All employees access various online systems and applications to handle their daily tasks. Customer service, order entry, inventory management, accounting, payroll and content management systems, just to name a few.
In addition, employees may surf the web for personal use, exposing their work computer to additional risks. If they click on a phishing email link from their personal email, they may be exposed to malware risks and identity theft.
Additional Cybersecurity Topics
Our comprehensive library includes other topics such as:
- Defining cybersecurity
- Passwords
- Protecting your mobile device
- Cybersecurity while traveling
- Types of malware
- Ransomware
- Email phishing
- Identity theft
- Social engineering
- Creating a cybersecurity training program
- Minimizing insider threats
- Protecting intellectual property
- Protecting your PC: Daily precautions
- GDPR

Watch Snippets of Cybersecurity Training Courses
From protecting your mobile devices to learning how to avoid phishing attempts, preview clips from our Cybersecurity topic here!

Additional Resources
- Tips for Creating a Cybersecurity Training Program
- How to Buy eLearning Content for Your LMS (And Not Regret it Later)
- Our Cybersecurity Training Topics
- Cybersecurity Training for Remote Employees [+Advice from a Training Company IT Director]
